Secure encrypted communication is the basis for a global connected mobile world. However, the closer quantum computers, ultra-powerful computers, come to a realistic reach, the more tangible the risks to IT security become. The American National Institute for Standards and Technology (NIST) has recognized these risks posed by quantum computers for secure data encryption and started a process to standardize quantum computer-resistant cryptographic methods in 2016 already.
Research groups from all over the world submitted concepts for new encryption methods, and 15 methods made it to the finals of the competition. Three out of four of the now finally accepted submissions were developed by researchers from the Cluster of Excellence CASA "Cyber Security in the Age of Large-Scale Adversaries" at the Ruhr-Universität Bochum (RUB), which has the goal of enabling sustainable IT security against large-scale, adversaries, in particular nation-state attackers. In doing so, they gained a worldwide recognized standardization competition that will significantly influence the quantum computer-resistant encryption methods of the future.
Secure encryption for tomorrow's computers
The standards certified by the federal agency are being adopted by numerous companies and online services, such as Amazon, Paypal and Google, based on experience, as they are considered particularly secure. "They represent better protection for digital communication - precisely because quantum computers would undermine previous encryption methods and signature systems," says Prof. Eike Kiltz, CASA spokesman and also a researcher in the procedure proposals CRYSTALS-KYBER and CRYSTALS-DILITHIUM. In addition to him, CASA Professors Tanja Lange, Peter Schwabe as well as Daniel J. Bernstein (former CASA PI) are involved in the selected methods. "The new NIST standard will certainly become one of the most influential documents in IT security," Eike Kiltz continues.
Data security in the quantum world
It is still uncertain, however, when the first powerful computers will actually start work. What is clear, however, is that "quantum computers can solve the two mathematical operations on which today's asymmetric cryptographic methods are based - making the current security infrastructure virtually worthless," says Prof. Peter Schwabe, CASA researcher and research group leader at the Max Planck Institute for Security and Privacy (MPI-SP).
For this reason, NIST began in 2016 to identify and eventually standardize suitable replacements for the current generation of encryption methods. This next generation of cryptographic algorithms is referred to as "post-quantum cryptography." NIST chose to use an open call for submissions of various approaches for this effort. Over the past five years, 69 proposals have been carefully analyzed for their security, efficiency, and other implementation characteristics.
The procedures now selected by NIST provide two different functionalities: The CRYSTALS-KYBER procedure enable secure key exchange over insecure communication channels such as the Internet. The SPHINCS+ and CRYSTALS-DILITHIUM procedures, known as digital signatures, are used to ensure the authenticity of data and senders. "The procedures developed show how important successful collaboration between basic research and application-oriented research is to ensure that the encryption of our data remains sustainably secure in the future," explains Eike Kiltz.
European authorities are likely to adopt NIST standardization
NIST is expected to set standards for the USA and Europe with its choice. "The European authorities are also still examining the procedures selected by NIST, but experience shows that they will agree with the assessment of their U.S. American colleagues if they do not find any security gaps," says Peter Schwabe. The reason for this is the encrypted data exchange between US. and European services, which would otherwise no longer be possible. Even though it will probably be several years before sufficiently large quantum computers are actually used - future encryption is secure with the methods developed in Bochum.
Algorithms to be standardized at a glance:
Public-Key Encryption/KEMs:
CRYSTALS-KYBER
Digital Signatures:
CRYSTALS-Dilithium
Falcon
SPHINCS+
Further Informationen
NIST Report on the Third Round of the NIST Post-Quantum Cryptography Standardization Process.
NIST press release.
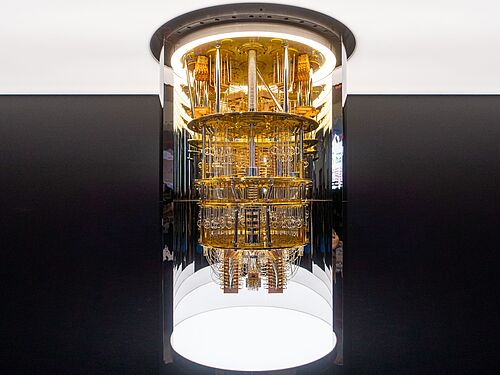
About quantum computers
Quantum computers are powerful computers. Classical bits, with which normal computers calculate, can only assume the values 0 or 1. In the quantum computer, qubits do this computing work: its processor, which uses the laws of quantum mechanics, works with qubits that are able to assume both values simultaneously. Certain operations, for which conventional computers would need tens of thousands of years, can thus be solved by quantum computers in just a few seconds. Previous encryption and signature methods are thus breakable and sensitive data would be unprotected.
Press contact
Prof. Dr. Eike Kiltz
Horst Görtz Institute for IT Security
Chair for Cryptography
Faculty of Computer Science
Ruhr-Universität Bochum, Germany
Phone: +49 234 32 25513
Email: eike.kiltz(at)rub.de
Prof. Dr. Peter Schwabe
Max Planck Institute for Security and Privacy (MPI-SP), Bochum
Radboud Universität, Nijmegen
Email: peter.schwabe(at)mpi-sp.org
General note: In case of using gender-assigning attributes we include all those who consider themselves in this gender regardless of their own biological sex.